AI Assisted
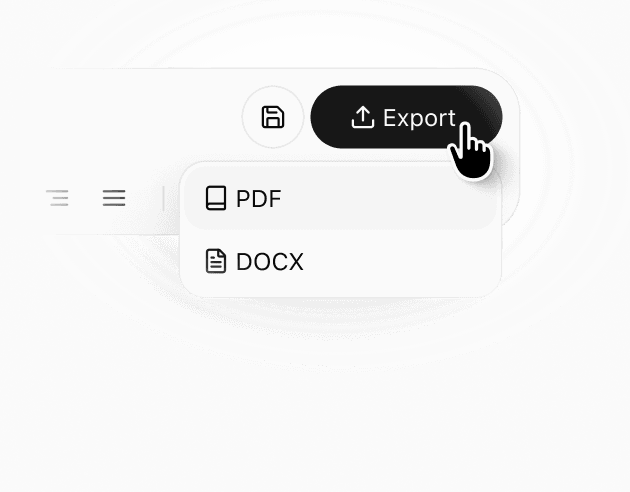
Export: PDF & DOCX
Get your custom agreement in minutes
4.8 Rating
Downloaded 2479 times
Get your complete
agreement in minutes
Select a template
Each template already follows legal structure and best practices.
Provide details
The agreement is automatically filled and adapted to your inputs.
Review & download
Check the generated document, make edits if needed, and download a ready-to-use agreement.
Details
Learn more about
Technical and Organizational Measures Template: Security Controls
TECHNICAL AND ORGANIZATIONAL MEASURES TEMPLATE FAQ
What are technical and organizational measures?
Technical and organizational measures, often called TOMs, are the safeguards an organization uses to protect personal data and the security of processing. Under GDPR Article 32, controllers and processors must implement measures appropriate to the risk, taking into account factors such as the state of the art, implementation costs, and the nature and scope of the processing.
Why do you need a technical and organizational measures document?
You need a technical and organizational measures document to clearly describe what security, access, governance, and response controls are in place. It helps with internal compliance, vendor review, customer due diligence, and data processing arrangements by showing how the organization protects confidentiality, integrity, availability, and resilience.
When should you use a technical and organizational measures document?
Use a technical and organizational measures document when an organization processes personal data and needs to explain its security controls to customers, vendors, auditors, regulators, or internal reviewers. It is especially useful during vendor onboarding, contract negotiations, privacy reviews, security questionnaires, and controller-processor compliance reviews.
How to write a technical and organizational measures document?
Start with the purpose, scope, and systems covered. Then describe the specific safeguards used for access control, encryption or pseudonymisation where appropriate, system security, backup and recovery, incident response, testing, and vendor management. Article 32 also specifically refers to measures such as pseudonymisation and encryption, the ability to ensure ongoing confidentiality, integrity, availability and resilience, the ability to restore access after an incident, and regular testing and evaluation of effectiveness.
Can AI Lawyer help if compliance, IT, and vendor reviewers all need to review?
AI Lawyer can help by organizing the document into clear sections so each reviewer can find the relevant details quickly. It can also add internal reference fields, review notes, and placeholders that make updates easier to track. A consistent layout helps reduce repeated edits and lowers the chance of missing key details like access controls, backup rules, incident procedures, or testing practices before the document is shared.
Similar templates